Digital government solutions provide the exact technical framework required to modernize public sector infrastructure. Government agencies process millions of identity verification requests every day. Administrators currently rely on outdated legacy systems to manage these massive data workloads.
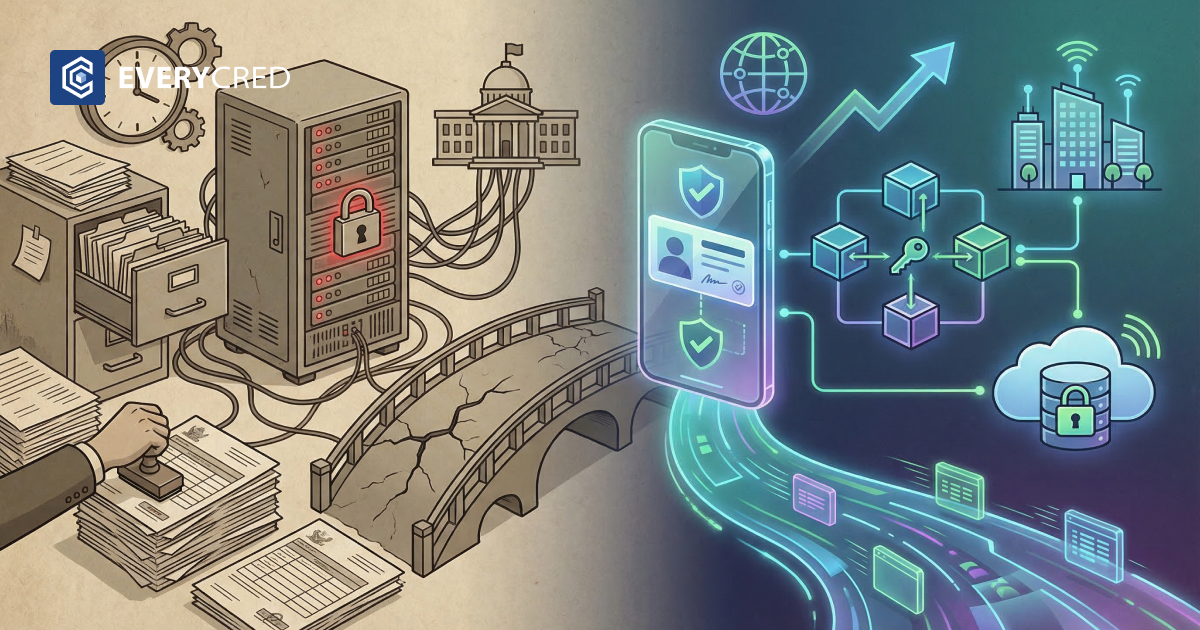
These legacy systems utilize centralized databases and physical paper records. This reliance creates severe bottlenecks in public service delivery. Processing delays frustrate citizens and drastically increase operational costs for the government.
Upgrading this failing infrastructure is the primary goal of digital government transformation. Agencies must transition away from physical document checks. They require secure digital verification methods. Implementing robust digital government solutions eliminates manual processing and secures citizen data against modern cyber threats.
The Failure of Legacy Systems in Public Administration
Public sector organizations face significant operational challenges with their existing identity infrastructure. Legacy systems force staff to perform manual data entry and visual document verification. These outdated processes consume thousands of staff hours annually.
- Data Silos: Government departments store citizen data in isolated databases. These systems do not communicate with each other. Citizens must submit identical information multiple times to different government agencies.
- Security Vulnerabilities: Centralized databases act as large targets for cyber attacks. A single successful breach exposes the sensitive data of millions of citizens simultaneously.
- Excessive Costs: Maintaining physical paper records and running outdated legacy servers requires massive annual budgets. Agencies spend more public funds on basic maintenance than on technological innovation.
- Fraud Susceptibility: Fraudsters easily forge paper documents and static PDF files. Manual inspectors frequently fail to detect sophisticated physical forgeries.
Digital government solutions replace these inefficient workflows. Administrators deploy new software platforms to automate the verification process and secure citizen records cryptographically. This technical upgrade drives true digital government transformation across all public sector services.
Read:
Digital Identity Models in the USA and India
Governments approach modernization differently based on their specific population needs and existing regulatory frameworks. The United States and India demonstrate two distinct methods for developing this infrastructure.
The United States Approach to Verification
The United States operates a highly fragmented identity system. State governments issue driver’s licenses. The federal government issues passports and social security numbers. This division complicates verification processes across different jurisdictions. Federal agencies utilize standards set by the National Institute of Standards and Technology (NIST) to unify these disparate systems. NIST provides strict technical guidelines for secure digital identity management. States currently develop mobile driver’s licenses based on these standards. These digital documents must meet strict interoperability requirements to function across state lines. Implementing standardized digital government solutions ensures these independent systems communicate securely.
India’s Population-Scale Infrastructure
India manages the largest biometric identity program in the world. The Aadhaar system provides a unique identification number to over a billion residents. This system forms the foundation of the India Stack, a comprehensive digital public infrastructure. The International Monetary Fund recognizes the India Stack for its direct role in expanding financial access and digital inclusion. India uses applications like DigiLocker to store digital versions of official documents. The current digital government transformation in India involves upgrading these static digital documents into mathematically provable, tamper-evident formats.
The Transition to Decentralized Identity
Modern public infrastructure requires a shift away from centralized control. Decentralized identity systems give citizens direct control over their personal data. Government agencies issue credentials directly to a citizen’s secure digital wallet. The citizen stores the data locally on their personal mobile device.
- Privacy Preservation: Decentralized identity infrastructure limits data tracking. The issuing government agency does not receive a notification or ping when the citizen uses the credential for verification.
- Selective Disclosure: Citizens choose exactly what data points to share. A citizen can prove they meet an age requirement without revealing their exact date of birth or home address to the verifying party.
- Reduced Liability: Government agencies no longer store massive honeypots of user data. This architectural change minimizes the legal and financial risks associated with large-scale data breaches.
Implementing decentralized identity requires new digital government solutions. These platforms connect the government issuer, the citizen holding the wallet, and the relying party requesting verification. This tripartite architecture secures the entire digital identity lifecycle.
Core Digital Government Solutions: Verifiable Credentials
Verifiable credentials function as the foundational building blocks of modern digital government solutions. A verifiable credential is a tamper-evident digital record. The issuing authority cryptographically signs the credential using a private key. This mathematical signature proves the exact origin and integrity of the data.
Public sector agencies issue verifiable credentials to digitize driver’s licenses, business permits, and welfare benefit allocations. The applications of verifiable credentials extend across all levels of municipal, state, and federal government operations. When a citizen presents a verifiable credential, the verifying agency uses public key cryptography to check the digital signature. The agency confirms the document is authentic and unmodified in milliseconds.
Technical Benefits for Government Operations
- Instant Verification: Automated systems verify mathematical proofs instantly. Staff members no longer manually inspect physical documents.
- Interoperability: Verifiable credentials follow global standards. A credential issued by a state health department works seamlessly with a federal tax agency system.
- Fraud Elimination: Cryptographic signatures make verifiable credentials impossible to forge. The verification software immediately rejects altered or expired data.
Deploying verifiable credentials is a mandatory technical step for building trust in public services. Citizens trust software that protects their privacy. Governments trust cryptographic proofs over easily forged paper documents.
Upgrading Systems for Digital Government Transformation
Agencies must execute a precise technical plan to replace legacy systems. Successful digital government transformation requires specific software upgrades. Departments must evaluate their current data issuance methods. Administrators select digital government solutions that integrate seamlessly with their existing databases.
Integration Steps for Agencies
- Assess Legacy Infrastructure: Identify exact bottlenecks in current verification processes. Determine which paper-based workflows cause the longest processing delays.
- Adopt Open Standards: Select digital government solutions that utilize open data standards. Avoid proprietary software that creates permanent vendor lock-in.
- Deploy Digital Wallets: Provide citizens with secure applications to store their digital identity data. Many government regions now utilize verifiable credentials stored in a digital locker to facilitate this secure local storage.
- Implement Cryptographic Verification: Train relying parties and integrated software systems to process decentralized identity proofs. Install API connections that read and validate cryptographic signatures automatically.
These technical steps ensure the government infrastructure supports the future of digital trust. Agencies that adopt these digital government solutions reduce their operational costs and processing times immediately.
Select Digital Government Solutions for the Public Sector
Public sector leaders require reliable enterprise technology to execute these necessary upgrades. The correct digital government solutions provide secure issuance, lifecycle management, and instant verification capabilities.
EveryCRED provides the exact enterprise-grade infrastructure required to facilitate this modernization. EveryCRED enables government agencies to issue mathematically secure, tamper-proof credentials directly to citizens. Our platform integrates directly with existing public sector databases via standard APIs.
Agencies use EveryCRED to eliminate manual document processing, secure citizen data from breaches, and establish a fully functioning decentralized identity ecosystem. It handles the complex cryptography automatically, allowing government staff to focus on service delivery rather than document verification.
Conclusion
Legacy systems severely limit public sector efficiency. Relying on physical documents and centralized databases exposes governments to extensive fraud and catastrophic security breaches.
Public administrators solve these critical infrastructure problems by adopting modern digital government solutions. Implementing decentralized identity models and verifiable credentials provides mathematical certainty to the verification process.
The transition to a secure digital identity framework protects citizen privacy and automates government services entirely. Government agencies must invest in proper digital government solutions to achieve complete modernization and secure the future of public administration infrastructure.

 19th March, 2026
19th March, 2026