Government agencies store citizen data in centralized databases. This structure creates centralized risk. Hackers target these single points of failure to steal personal information. Innovation teams in the USA and India must secure their data infrastructure against these attacks.
Decentralized identity offers a direct technical solution. This implementation roadmap explains how governments can build, test, and deploy these new systems. The process requires new technical standards, cryptographic verification, and careful policy planning.
Why Do Centralized Government Databases Fail to Protect Citizen Data?
Centralized architectures store millions of records in one location. This data model creates a high-value target for cyber-attacks. Decentralized identity removes this single point of failure by distributing data control to the individual citizen.
- Single Points of Failure: One database breach compromises millions of citizens simultaneously.
- Costly Incident Recovery: Agencies spend millions of taxpayer dollars resolving identity theft and system downtime.
- Lack of Citizen Control: Citizens cannot monitor who accesses their data or restrict unauthorized sharing.
- High Maintenance Costs: Securing giant data silos requires constant hardware upgrades and security patches.
Governments must upgrade their security models to protect national security. Implementing digital identity verification with verifiable credentials reduces unauthorized access. This method forces systems to verify the mathematical proof of the data rather than checking a centralized database.
How Does Digital Identity Blockchain Secure National Infrastructure?
A digital identity blockchain distributes data verification across a wide network of computer nodes. It does not store personal citizen data on the public ledger. It stores public keys, decentralised identifiers, and cryptographic proofs.
- Data Immutability: System administrators and external hackers cannot alter records without immediate detection by the network.
- Decentralized Control: No single agency controls the entire network infrastructure. Multiple departments operate different nodes.
- Cryptographic Trust: Mathematics verify transactions and data authenticity, replacing manual administrative checks.
- High Availability: If one server fails, the rest of the digital identity blockchain continues to process verifications.
The World Wide Web Consortium (W3C) published the Decentralized Identifiers (DIDs) v1.1 specification. This document defines how software systems create and resolve decentralized identifiers globally. Government technical teams use these exact standards to build resilient networks. A digital identity blockchain ensures these identifiers remain available and tamper-evident at all times.
How Do Verifiable Credentials Change Citizen Verification Processes?
Verifiable credentials digitize physical documents. Examples include driver’s licenses, tax identification numbers, and professional licenses. They use public key cryptography to prove authenticity and origin.
- Cryptographic Signatures: The issuing government agency signs the digital document mathematically using a private key.
- Tamper-Proof Format: Any alteration to the document invalidates the mathematical signature immediately.
- Offline Verification Capabilities: Scanners and mobile devices can verify documents without an active database connection.
- Selective Disclosure: Citizens share only specific data points. A citizen can prove they are over eighteen without revealing their exact birth date or address.
Citizens hold their data on their own mobile devices or hardware security modules. They use digital identity wallets to store and present these documents. The wallet software communicates with government verification portals to prove identity claims.
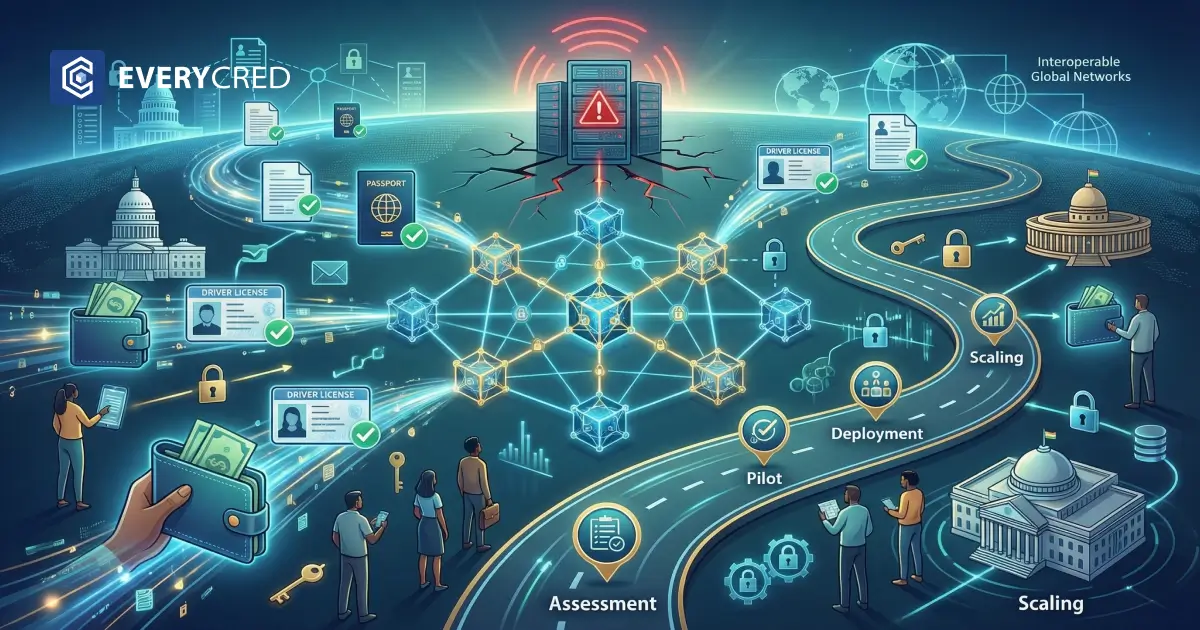
What Is the Step-By-Step Implementation Roadmap for Government Teams?
Implementing decentralized identity requires a phased approach. Government agencies cannot replace legacy systems overnight. Innovation teams must follow a strict deployment schedule.
Phase 1: Technical And Policy Readiness Assessment
- Inventory all existing database dependencies and legacy identity providers.
- Identify high-risk identity services that require immediate security upgrades.
- Draft strict policies for cryptographic key management and key rotation.
- Define the Level of Assurance (LOA) required for specific digital government services.
Phase 2: High-Impact Pilot Program Selection
- Select a single, distinct use case. Examples include issuing digital employee IDs or specialized medical licenses.
- Define concrete success metrics for the pilot program, such as verification speed and failure rates.
- Limit the initial user base to a controlled group of internal employees or specific contractors.
- Test the issuance, presentation, and revocation processes for verifiable credentials under controlled conditions.
Phase 3: Infrastructure Deployment and Integration
- Deploy the underlying digital identity blockchain nodes across multiple secure government data centers.
- Integrate the new credential issuing engine with existing legacy identity databases via secure APIs.
- Establish secure, encrypted communication channels between data issuers, citizen holders, and government verifiers.
- Run stress tests to ensure the system handles high transaction volumes during peak tax or voting seasons.
Phase 4: Citizen Onboarding and System Scaling
- Launch public awareness campaigns explaining the mechanics of the new system.
- Provide secure applications for citizens to manage their digital identity on major mobile operating systems.
- Establish dedicated support channels for technical issues and lost device recovery.
- Expand the system to include complex services. Agencies must plan for long-term integration to achieve digital trust and verifiable credentials.
How Can Agencies Manage Cross-Border Identity Interoperability?
Citizens travel and conduct business across different states and international jurisdictions. A digital identity must function outside its original issuing region. Innovation teams in the USA and India face different regulatory environments and federal structures.
- Global Standard Adoption: Agencies must adopt universal data formats to ensure different software systems can read the data.
- Mutual Recognition Agreements: Governments need formal agreements to recognize cryptographic signatures from foreign agencies.
- Open-Source Protocols: Proprietary software systems block cross-border integration. Teams must use open standards.
The Government of India highlighted the importance of interoperable systems in its G20 Policy Recommendations for Digital Public Infrastructure. Scalable public systems require shared technical foundations. Decentralized identity provides this exact foundation by standardizing how data is packaged and verified.
What Are the Technical Requirements for Credential Issuance?
Agencies need specific software components to issue and verify data accurately. The infrastructure must operate continuously without interruption.
- Issuance Engine: This software connects to legacy databases. It formats citizen data into verifiable credentials and applies the government’s cryptographic signature.
- Verification Engine: This software reads incoming cryptographic signatures. It checks mathematical validity and queries revocation registries.
- Revocation Registry: This system invalidates lost, stolen, or expired credentials. It updates the ledger so verifiers know to reject the document.
- Trust Framework Policy: A defined set of technical rules governing which specific agencies can issue specific credential types.
Understanding the difference between legacy security certificates and modern cryptographic proofs is a mandatory technical requirement. Agencies must transition from outdated formats to verifiable digital certificates to ensure maximum security against forgery.
How Do Governments Mitigate Vendor Lock-In with Blockchain Systems?
Government contracts often result in long-term dependence on single software vendors. This limits future software upgrades and increases operational costs.
- Mandate Open Standards: Require the use of W3C and FIDO standards in all procurement documents and requests for proposals.
- Ensure Data Portability: Ensure the government agency can extract cryptographic keys, issuer profiles, and data schemas at any time without vendor permission.
- Distribute Node Operators: Distribute digital identity blockchain nodes across different cloud providers and on-premise government servers.
Decentralized identity systems prevent vendor lock-in by mathematical design. The architecture separates the standardized data format from the specific software applications that process it.
How Can EveryCRED Support Your Identity Modernization Project?
Transitioning to decentralized identity requires robust issuing and verification technology. EveryCRED provides enterprise-grade infrastructure built specifically for government innovation teams.
Our platform issues verifiable credentials that comply strictly with global W3C standards. EveryCRED integrates directly with existing legacy databases, preventing system downtime during deployment.
Our systems operate on secure digital identity blockchain networks, ensuring data immutability and high availability. Government agencies use our solution to eliminate centralized risk, automate credential verification, and deploy scalable digital identity solutions.
Contact our technical team to schedule an infrastructure assessment and pilot program consultation.

 20th March, 2026
20th March, 2026